THIS LAST JUNE 10, 2015 in the wake of 4 million people having their data stolen, we did a blog post that addressed a crisis of data and identity theft. From that time until August 11, according to the Identity Theft Resource Center, another 124 data breaches have occurred (something like 2 each day) and another 32 million records have been compromised, bringing the total for 2015 (just 2015! so far!) to 472 breaches and 139,278,685 people’s records. By the time you read this. there will be millions more.
Are you one of them? Do you know for sure? Sometimes when a company notifies you of a data breach, the letter they send could be (and often is) mistaken for junk mail and tossed out. Here’s a way to find out: The New York Times ran a story – “Data Loss – Were You Affected?” – that will help you discover whether your data is among the stolen. Do read the article below, and make sure to click through to see your own results.
From the New York Times:
Half of American adults had their personal information exposed to hackers last year alone. In a recent attack at the federal Office of Personnel Management, hackers stole the most sensitive personal data for 21.5 million people.
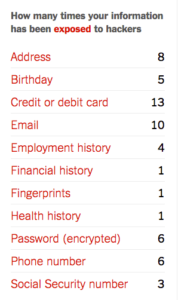
[Answer a few questions here, and you might find out how many times your sensitive information may have been stolen. Note that this quiz covers just the major breaches. Even if nothing shows up for you on this list, your data may have been grabbed in some smaller theft.]
[If you find your data has been stolen] What should you do now?
Review your account statements for any fraudulent purchases, as well as your credit report. Make sure you have different passwords for different accounts: in particular, don’t use the same password for your bank accounts, email and e-commerce accounts.If you were the victim of more than one breach, some security experts recommend freezing your credit. To do so, call Equifax, Experian or TransUnion and ask to have your account frozen. The credit agency will mail you a one-time PIN or password to unfreeze your account later. If you plan on applying for a new job, renting an apartment or buying insurance, you will have to thaw a freeze temporarily and pay a fee to refreeze the account.
Why does this keep happening?
The Internet was built for openness and speed, not for security. As more and more services, infrastructure and personal information move online, they have all become targets for hackers, who constantly scan the Internet for potential security holes and entry points.At government agencies, old, out-of-date systems and budget shortfalls have left information vulnerable. Security experts say there is no way to keep hackers out of systems with traditional defenses like firewalls and antivirus software.With breaches now the norm, organizations are finally moving towards more modern defenses, like monitoring software that can pick up unusual network activity and two-factor authentication, a system that requires employees and Internet users to enter a second, one-time password when they log in from a new computer. But security experts say the only way information can be protected is to scramble it with encryption technology that makes it unreadable to hackers.
How can you protect yourself from stolen data in the future?
It’s pretty simple: You can’t. But you can take a few steps to make things harder for criminals. Turn on two-factor authentication, whenever possible. Most banking sites and ones like Google, Apple, Twitter and Facebook offer two-factor authentication. Change your passwords frequently and do not use the same password across websites. Vigilantly monitor your bank accounts and credit report. Do not enter sensitive information into websites that do not encrypt your connection. Look for a lock symbol next to the web address whenever entering sensitive information and do not enter it if you cannot see the lock symbol.
Take this interactive quiz from The New York Times to evaluate whether your information may have been compromised, and learn more about individual breaches.
In conclusion:
As we mentioned back in June, you can’t do much to proactively protect yourself if your employer or your health plan suffers a breach. But all those other people who sell you things collect information about you, and you can do something about that.
You need to manage what your share and to whom you share it with. Control your data streams and only provide information about yourself that facilitates your ability to manage the digital relationship for your benefit. And when you’re signing up for anything, watch out for any box that’s already checked … chances are it’s asking for permission to gather more information, share your data with affiliate companies, or to send you something. Caveat emptor.
Cheers,
David
Also: Has a company violated your privacy? Check out today’s companion post: Did a Company Share Your Information W/O Your Consent? The FTC Wants to Know.